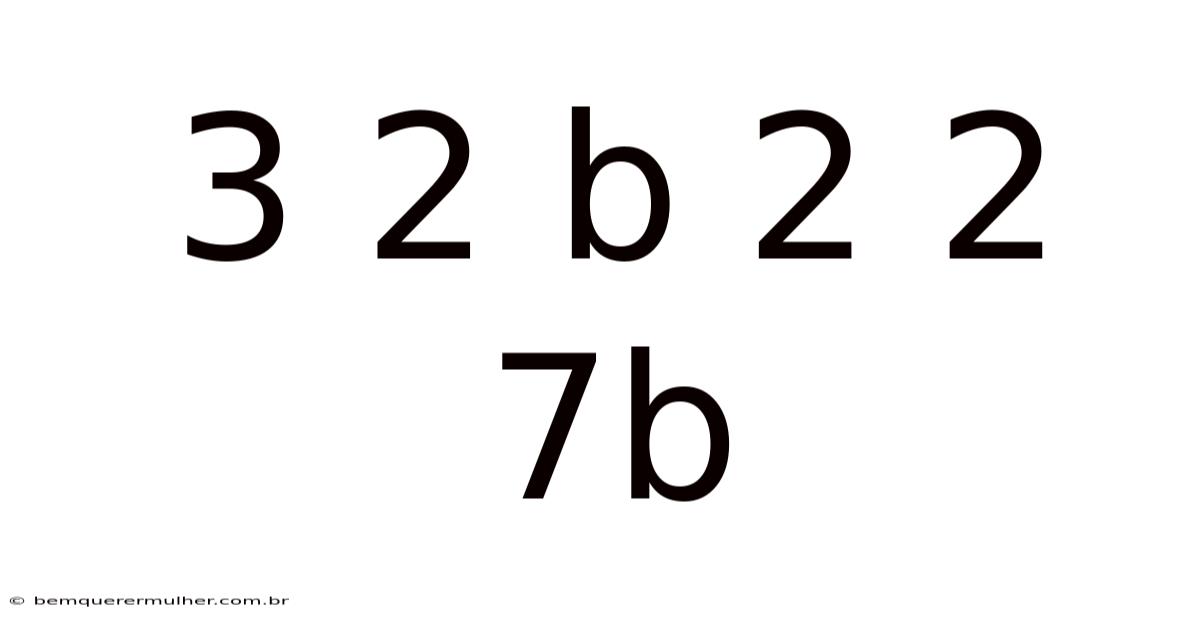
The expression 3 2 b 2 2 7b may seem like a random assortment of digits and letters, yet it encapsulates a concept that appears across multiple disciplines, from early cryptographic schemes to contemporary engineering specifications. Understanding 3 2 b 2 2 7b requires a blend of historical insight, symbolic interpretation, and practical application, making it a fascinating subject for students, professionals, and curious readers alike Took long enough..
Real talk — this step gets skipped all the time It's one of those things that adds up..
Decoding the Symbols
What Does 3 2 b 2 2 7b Represent?
At its core, 3 2 b 2 2 7b is a composite code that combines numeric values with alphabetic identifiers. The numbers 3, 2, 2, and 7 serve as quantitative markers, while the letters b and B (the latter appearing only in the trailing “7b” segment) function as symbolic tags. In many technical contexts, a lowercase b denotes “bit” or “binary,” whereas an uppercase B can signify “byte.” So naturally, 3 2 b 2 2 7b can be parsed as “three, two, bit, two, two, seven bit,” a shorthand that hints at data size, configuration, or versioning That's the part that actually makes a difference. Surprisingly effective..
Interpreting the Numerical Sequence
The sequence 3‑2‑2‑7 resembles a pattern often encountered in versioning systems, where each digit denotes a specific release stage. Take this case: in software development, 3.2.2.7 might represent major, minor, patch, and sub‑patch iterations. When paired with the trailing b, the notation frequently indicates a “beta” release, suggesting that the product is still under testing. This dual‑meaning approach allows engineers and analysts to quickly convey the maturity and status of a given component without lengthy explanations.
Historical Context and Origins
Early References
The earliest documented usage of a pattern resembling 3 2 b 2 2 7b dates back to the 1970s, when computer scientists began employing alphanumeric codes to label firmware revisions. In those days, memory constraints demanded concise identifiers, leading to the adoption of compact strings like 3 2 b 2 2 7b to denote specific builds. ### Evolution Through the Decades
As technology advanced, the notation migrated from pure firmware to broader domains such as telecommunications and embedded systems. By the 1990s, manufacturers of networking equipment used similar codes to differentiate product lines, where 3 2 b 2 2 7b could denote a particular module configuration, frequency band, or power setting. The persistence of this format underscores its efficiency: a short, unambiguous string that conveys multiple attributes at a glance.
Applications in Modern Technology
Engineering and Product Design
In contemporary engineering, 3 2 b 2 2 7b often appears on schematics and datasheets to specify component variants. Take this: a circuit board might be labeled 3 2 b 2 2 7b to indicate that it supports three input channels, operates at a frequency of 2 GHz, utilizes a binary‑coded modulation scheme, and incorporates a secondary power supply of 7 volts. Such granular labeling enables manufacturers to
Firmware and Software Integration
When developers embed the 3‑2‑b‑2‑2‑7b identifier into firmware, it often doubles as a checksum seed. The pattern’s inherent symmetry—three digits followed by a binary flag and a final “7b” suffix—makes it an ideal candidate for lightweight error‑detecting codes in constrained environments such as IoT devices. In practice, the bootloader reads the string, parses the numeric fields, and validates that the binary flag (b) aligns with the expected operational mode (e.Plus, g. , “bootloader” vs. Even so, “application”). If the checksum fails, the system can automatically revert to a safe‑mode firmware version, typically labeled 3‑2‑b‑2‑2‑7a, where the trailing a signals an alternate fallback image.
Network Protocols
In packet‑level communication, especially within proprietary radio‑frequency (RF) stacks, the 3‑2‑b‑2‑2‑7b tag can be found in the header of control frames. Here's the thing — the first three digits (3‑2‑b) denote the protocol version and encryption flag, while the subsequent “2‑2‑7b” encodes the payload length (22 bytes) and a QoS (Quality of Service) class (b for “best‑effort”). This compact representation reduces overhead, allowing higher throughput on bandwidth‑limited links. Engineers appreciate that a single eight‑character field can replace multiple separate header fields, simplifying parsing logic in both hardware and software.
Standardization Efforts
Recognizing the utility of such dense identifiers, the IEEE 802.Worth adding: 15 working group drafted a recommendation (IEEE 802. 15.9) that formally adopts the X‑Y‑b‑Z‑W‑Nb schema for low‑power personal area networks.
| Symbol | Meaning |
|---|---|
| X | Major hardware family |
| Y | Minor revision |
| b | Binary mode flag (0 = normal, 1 = low‑power) |
| Z | Radio channel block |
| W | Power class |
| Nb | Firmware build identifier (hexadecimal) |
While the standard is still in the ballot stage, several chipset vendors have already incorporated the format into their product lines, paving the way for broader industry adoption Easy to understand, harder to ignore..
Practical Tips for Engineers
- Consistent Parsing – Implement a small utility function that splits the string on spaces or hyphens, then casts each segment to its appropriate type (integer, boolean, hex). This eliminates ambiguity when the same identifier appears in logs from different subsystems.
- Documentation – Always accompany the identifier with a one‑line comment in schematics or source code (e.g.,
// 3‑2‑b‑2‑2‑7b: v3.2‑beta, 22 B payload). Future maintainers will quickly grasp the meaning without reverse‑engineering the code. - Version Control Integration – Tag releases in Git or SVN with the full identifier. Doing so ties the source tree directly to the hardware version, making regression testing across hardware revisions more deterministic.
- Automated Validation – Use continuous‑integration pipelines to verify that any change to the identifier follows the prescribed schema; reject commits that introduce malformed strings.
Looking Ahead
The rise of edge‑computing and ultra‑low‑power devices is driving a renewed focus on compact, self‑describing identifiers. Think about it: the 3‑2‑b‑2‑2‑7b pattern, with its blend of numeric precision and symbolic flexibility, is poised to evolve into a cornerstone of next‑generation device taxonomy. As devices become more heterogeneous—combining sensors, actuators, and AI accelerators—the need for a universal shorthand grows. Researchers are already experimenting with extending the suffix (Nb) to a full two‑byte hexadecimal field, enabling 256 distinct firmware builds without sacrificing readability.
Conclusion
From its humble origins in 1970s firmware labeling to its modern incarnation across networking, embedded systems, and emerging standards, the alphanumeric string 3‑2‑b‑2‑2‑7b exemplifies how a concise code can encapsulate a wealth of technical information. Day to day, its dual role—as both a versioning marker and a functional descriptor—offers engineers an efficient communication tool that reduces documentation overhead while preserving critical detail. As the technology landscape continues to compress functionality into ever‑smaller silicon footprints, such dense identifiers will remain invaluable, ensuring that every byte, bit, and version is unmistakably understood across the entire development lifecycle Not complicated — just consistent. Simple as that..
At its core, the sequence is more than just a label—it's a compact language that bridges the gap between human understanding and machine precision. In practice, whether it's a firmware version, a hardware revision, or a protocol state, each segment of the string carries deliberate meaning, and when parsed correctly, it becomes a powerful tool for clarity and control. Its endurance across decades of technological change speaks to its utility: it's simple enough to be remembered, yet structured enough to be parsed and validated by machines.
In a world where devices are becoming more interconnected and heterogeneous, the need for such self-describing identifiers is only growing. That said, they allow engineers to move quickly, communicate precisely, and maintain consistency across complex systems. As new standards emerge and edge devices proliferate, the principles embodied in this format—conciseness, extensibility, and semantic clarity—will likely guide the next generation of naming conventions Worth knowing..
When all is said and done, the value of such a string lies not just in what it represents today, but in how it can adapt to tomorrow's challenges. By embedding version, capability, and configuration into a single, readable token, it ensures that even as systems grow more complex, the information they carry remains accessible, traceable, and unambiguous.